Centralized Event Log Management, Syslog, SNMP and Performance Monitoring
In today’s complex and ever-evolving IT landscape, the efficient management and monitoring of daily operations are paramount for organizations to ensure their systems run smoothly, securely, and without disruptions. Event log management tools have emerged as indispensable allies in this endeavor, enabling businesses to gain real-time insights, detect anomalies, and troubleshoot issues swiftly.
Bring Together All Your Logs & Events
ELM Enterprise Manager lets you collect log and event data from all of your servers, systems, firewalls, devices and applications across your IT infrastructure and presents that ocean of information in a standardized format. Whether you have a single location or multiple, ELM has the scalability and secure communications to handle virtually any environment.
- Consolidate data from Windows Events, Syslogs, SNMP
- Standardize your data into unified format
- Filter, aggregate and analyze events that matter to you
- Categorize systems or locations for easy organization
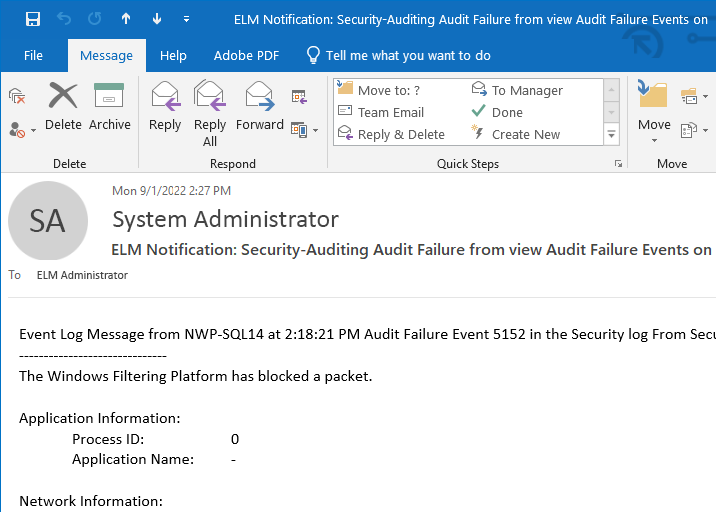
- Get real-time alerts and automate follow-up actions
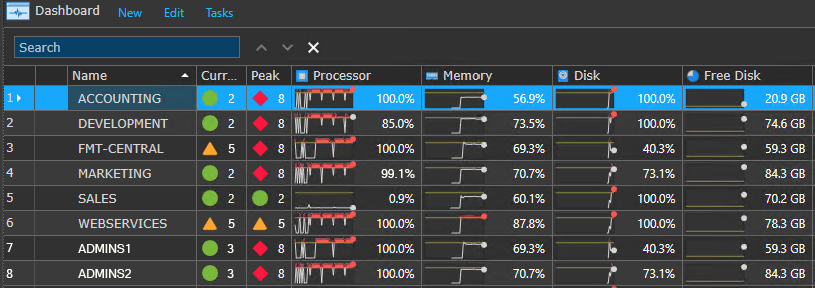
Monitor Performance & Availability
Combine your log management with performance metrics and system availability monitoring for a complete view of infrastructure.
- Detect bottlenecks and potential issues
- Processor, Memory, Disk, Free Disk, Network and More
- Correlate events to performance measures
- Monitor end-to-end system availability & processing
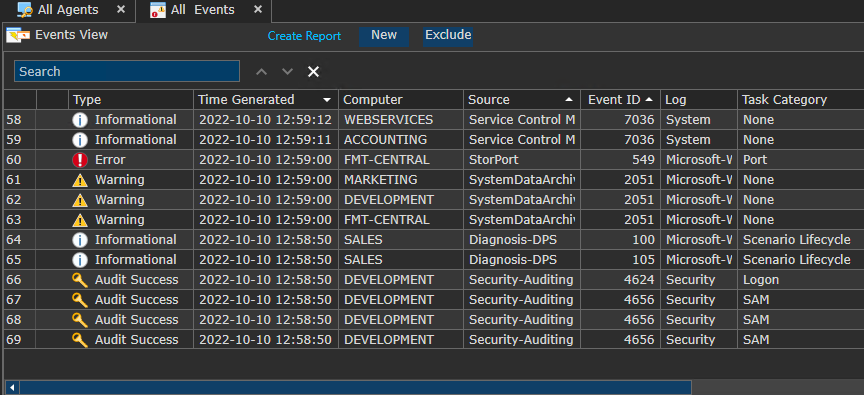
Event Views & Filters
Event Views provide a near real-time look into data collected and are grouped into various different displays utilizing both include and/or exclude filters. ELM comes pre-configured with a number of Event Views for investigation into system activity, security events, cause-effect relationships through correlation and much more. Custom Event Views are easy to create and highly customizable to your specific viewing and notification needs.
ELM’s Event Views also include powerful filtering on-the-fly across multiple column headings as well as an advanced search feature making it a powerful resource for pinpointing specific events and details.
Going beyond the viewing of data, ELM’s advanced capabilities provide the ability to filter clear down to the agent or collection level, streamlining event data processing while minimizing storage requirements.
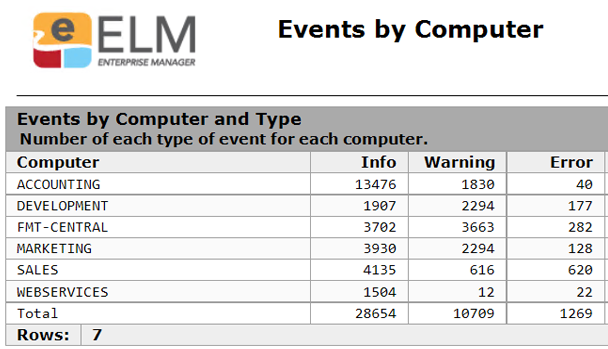
Reporting & Archiving
Support a variety of compliance mandates by consolidating your standardized event data with secure storage in Microsoft SQL Databases. ELM provides a well designed database strategy so that not a single event is missed.
- Primary Database for daily operations
- Failover Database for fault tolerance
- Archive Database options for longer term storage
- Dozens of reports included for aggregate views of event activity
- Custom Reports available for your specific needs

Fault Tolerance
Even with the best hardware, operating systems and virtualization, downtime or connectivity issues still happen. ELM Enterprise Manager has multiple layers of fault tolerance built into the product to prevent data loss and make data collection recovery one less problem you have to deal with during an outage.
- Agent level caching of events when connectivity to the ELM Server is interrupted.
- The ELM server will automatically swing over to a (local) failover database when the primary database is unavailable.
Once normal operations are restored, ELM will automatically merge all data collected back to the primary database (like it never happened).
Scalability & Architecture
No matter the size or scale of your monitoring and alerting needs, ELM Enterprise Manager is designed to handle it. Multiple sites, multiple locations, multiple networks, n-tier architectures, it’s all in a days work.
- Installations from a handful to hundreds of devices
- Support for physical, virtual and and legacy operating systems
- Event forwarding for centralization or data sharing from remote locations

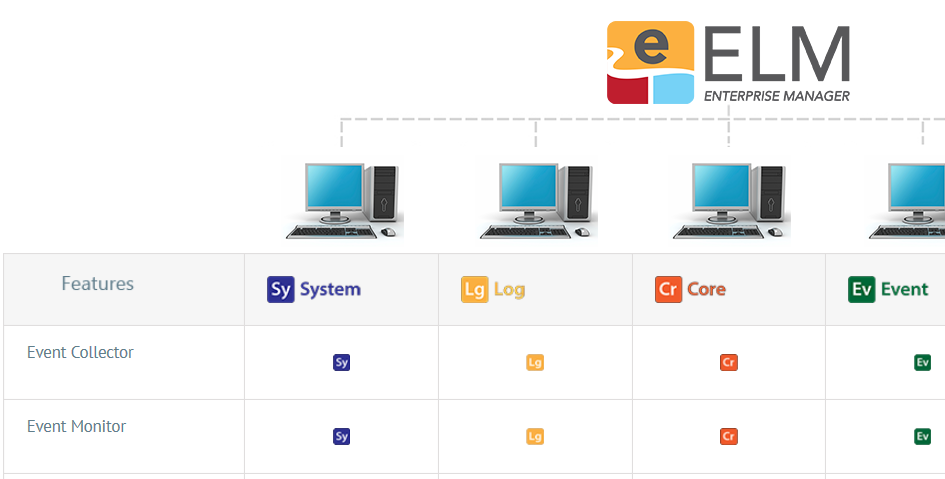
Flexible Licensing by Design
ELM provides five products (licenses) in one. Our flexible licensing model allows you to select the monitoring features you need, and skip those you don’t. Think of ELM’s capabilities and licenses like a menu – you order the combination of features that best suits your server, workstation or network device’s appetite.
- One enterprise platform with many options.
- Design your monitoring solution based on your actual needs.
- Use different standard configurations for different machines.
- Create a budget friendly solution.