Server Monitoring &
Event Log Management
With thousands of installations over the last 25+ years, ELM Enterprise Manager is the trusted solution for your
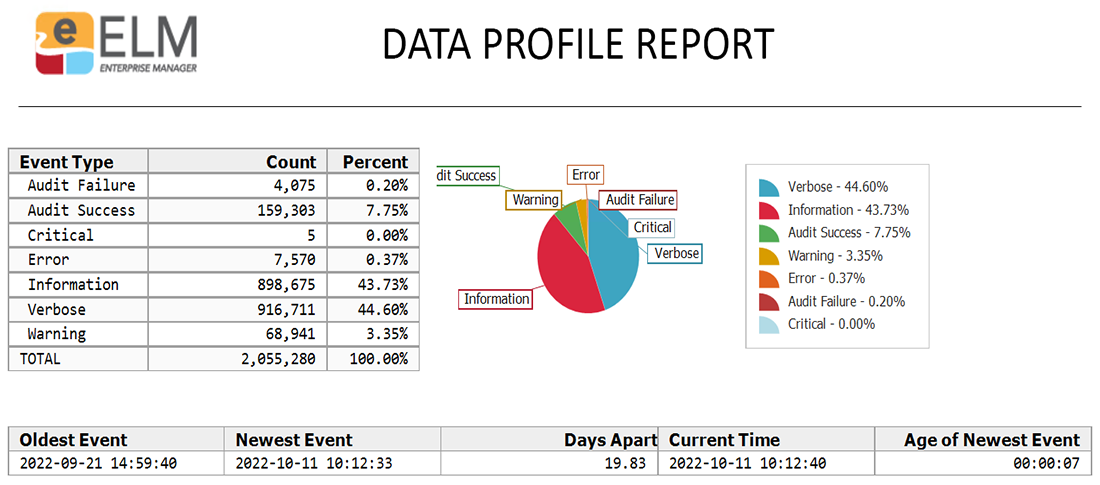
event log collection, server & device monitoring, real-time notifications and reporting.
Calling all System Administrators and IT Managers >> Keep security events or performance issues from turning into downtime or loss of revenue with continuous monitoring and alerting of your critical systems, switches, firewalls and applications.
Industries Served
Supporting time-sensitive and mission critical operations around the globe.Mission Critical Operations & Networks
Key Features
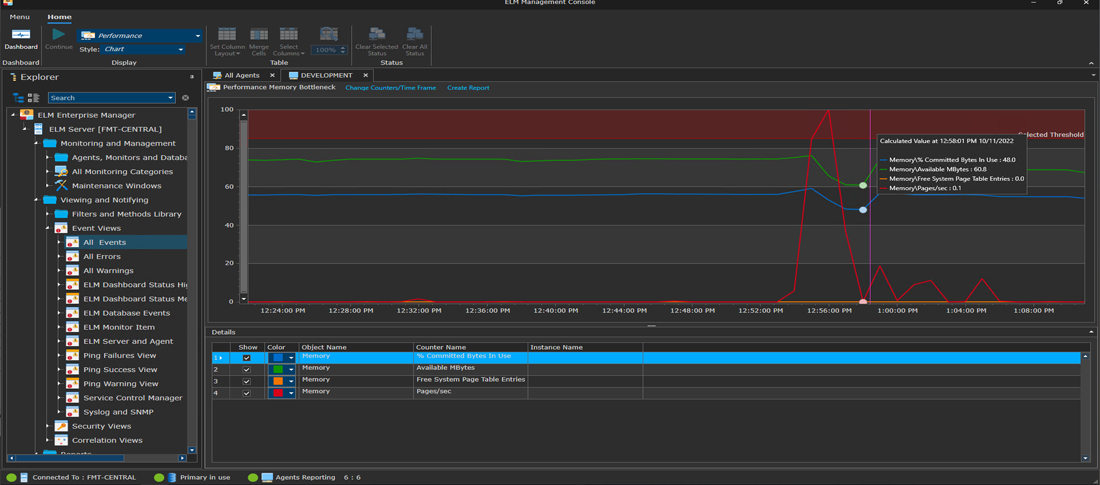
Explore ELM's extensive monitoring, alerting and reporting features.System Monitoring and Management
Licensing Options
Flexibility to build a monitoring solution to fit your specific needs and budget.Five Products Under One Umbrella
- Servers, Workstations & Devices
- Mix & Match Feature Sets
- Perpetual or Subscription Plans
- Forward Events To Central Servers
- Volume Discounts
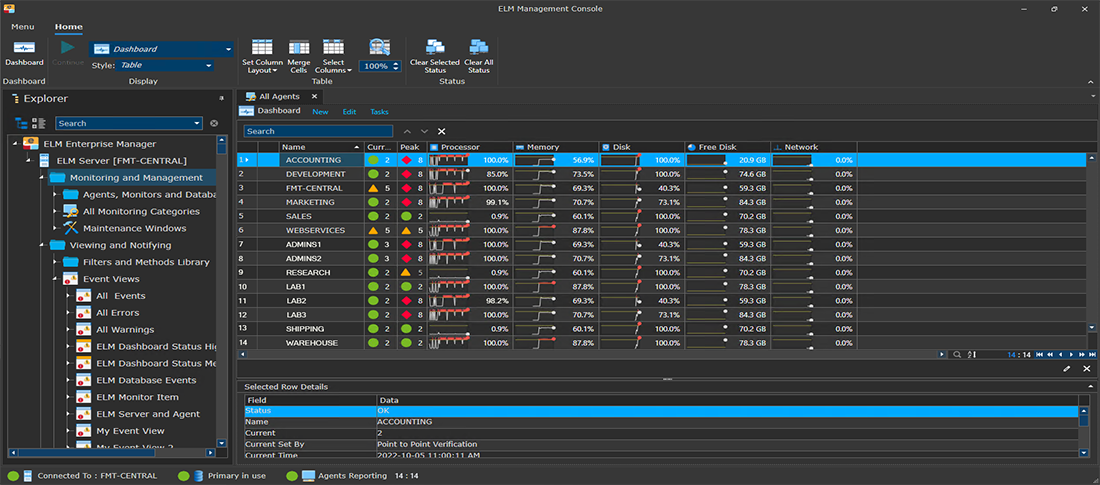
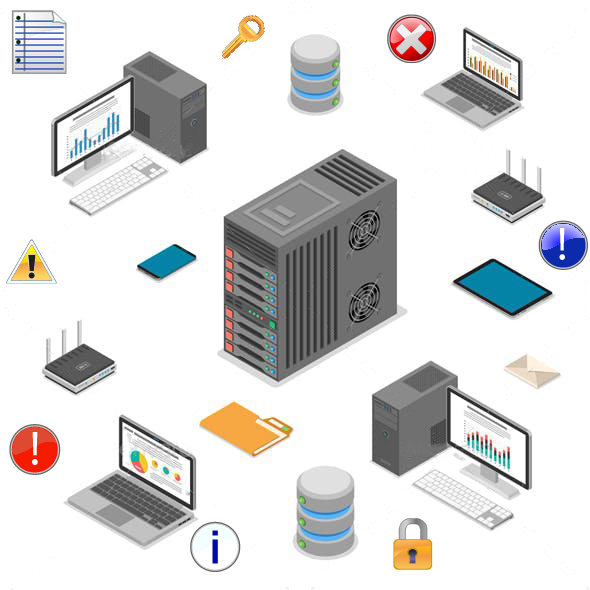
Centralized Monitoring for Windows Events, Application Logs, Syslog & SNMP
ELM Enterprise Manager allows you to quickly and easily keep watch on the things that matter most in your network. It is highly customizable to handle anything from the latest in virtualization technology, any non-circular log file source, and even older or legacy operating systems that are still going strong.
Smart Monitoring Software. Endless Possibilities. ELM Enterprise Manager.
ELM v8.0 Details
See What's New in ELM Version 8.0
Our team has been hard at work to bring you an entirely new experience for your event log management and server monitoring needs. ELM has been completely redesigned with new enhancements and performance features that will satisfy the needs of any size network. Check it out today!
ELM v8.0 Details